Friday Hacks #291, March 13: From Wondering to Space and CPU Security Vulnerabilities
Posted on by Jeya
Date/Time: March 13 at 7:00pm SGT
Venue: Seminar Room 12, COM3-01-21, NUS
Sign-up Link: NUSync | Luma
Food 🍕 and Drinks 🧋 will be served!

1) Twinkle Twinkle Little Star, How I Wonder Myself to Space
Zhen Ning will be sharing how he ended up building a space company in Singapore and a little about the technical challenges faced along the way. He would be sharing his life experiences and how wondering about things got him into this field.
Speaker Profile 🎙️
Zhen Ning Ng graduated from NUS with a degree in Engineering Science Programme. Upon graduation, he worked at DSO National Laboratories before returning to NUS as a Research Engineer working on cubesatellites. In 2018, NuSpace was founded with a mission to provide affordable connectivity to remote locations.
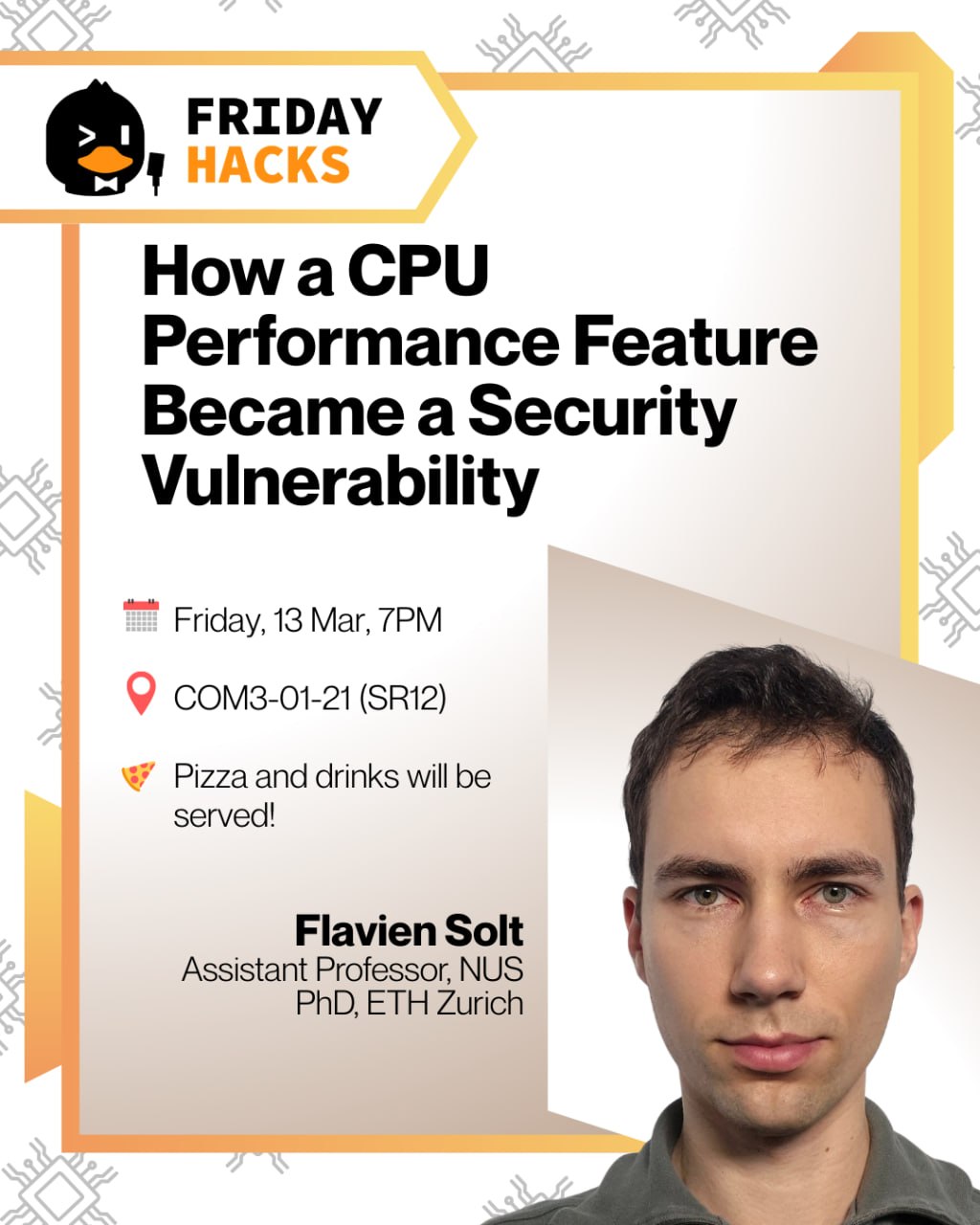
2) How a CPU Performance Feature Became a Security Vulnerability
Modern CPUs are built for speed. To run programs faster, they also predict, speculate, and start work early. Features such as pipelining, caching, and branch prediction are what make modern processors so efficient – but these same features can create surprising security problems. The talk covers basic architectural ideas behind modern processors, how speculative execution helps CPUs run quickly, and how attackers can turn these mechanisms against the system using transient execution attacks such as Spectre. The final part discusses finding new vulnerabilities using model-based relational testing, including a discovery that triggered a nearly two-year embargo period while hardware vendors prepared mitigations.
Speaker Profile 🎙️
Flavien Solt is an Assistant Professor at the National University of Singapore. Previously, he was a postdoctoral researcher in the SLICE Lab at UC Berkeley, working with Chris Fletcher. He received his PhD from ETH Zurich in 2024, was recognized with the ETH Medal, under the supervision of Kaveh Razavi, working on software-inspired techniques for hardware security.
👋 See you there!